Google-backed file sharing program spreads malware to Windows and Android users
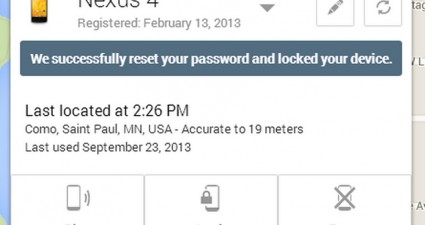
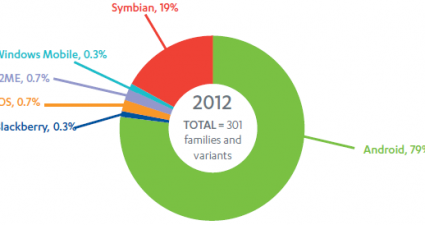
If you’re from the West, then you might not have heard of Xunlei, a popular BitTorrent client in China. Aside from delivering entertainment to its users, the BitTorrent client is also distributing malware to Windows PCs and Androi...