 If you think that the level of security that your current email provider provides is not enough to secure your important email messages, you might as well encrypt them using the OpenPGP standard. Speaking of which, this is a process that you can easily do using InstantCrypt, a free email encryption program.
If you think that the level of security that your current email provider provides is not enough to secure your important email messages, you might as well encrypt them using the OpenPGP standard. Speaking of which, this is a process that you can easily do using InstantCrypt, a free email encryption program.
What Is It and What Does It Do
Main Functionality
InstantCrypt is an email encryption program that allows you to send and receive encrypted emails. This process involves data encryption and decryption using the OpenPGP standard. Through this program, you get to have a secure end-to-end encryption system that you can use on your preferred web mail service or email program.
Pros
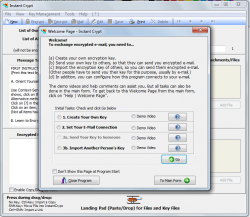
- Provides a detailed tutorial for new users, you can also refer to the Help Page to learn how the program works
- Uses OpenPGP method to encrypt and decrypt messages
- Provides a secure end-to-end user encryption system
- Secures your emails using a unique passphrase or password
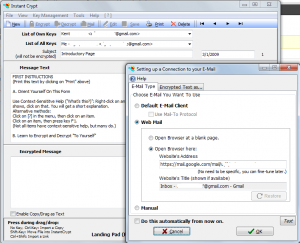
- Supports all common types of email programs or web email services (Gmail, Yahoo Mail, Outlook/Hotmail, etc.)
- Supports file attachments – text files, documents, photos, audio files, etc.
- Keyfile backup – lets you create a backup copy of your key files
- Offers a portable version
- You can easily decrypt your emails using other OpenPGP programs, if you no longer want to use InstantCrypt
Cons
- May not be suitable to all users especially those who don’t have basic knowledge about encrypting or decrypting files
- You cannot send your emails to multiple recipients
- The location or folder where your key files are stored aren’t protected
Discussion
 InstantCrypt is useful especially if you want to make sure that no one else could read your emails except for the original recipient. While most of today’s email services are already secured with different security and encryption methods, it is still better to add another layer of security and that is through the use of the OpenPGP encryption method.
InstantCrypt is useful especially if you want to make sure that no one else could read your emails except for the original recipient. While most of today’s email services are already secured with different security and encryption methods, it is still better to add another layer of security and that is through the use of the OpenPGP encryption method.
Through this program, you can send and receive email messages that are encrypted. This also means that in order for you to decrypt the message, you’ll need to provide the correct key as well as the correct passphrase. In the same manner, your recipients won’t be able to decrypt your email message unless they have your PGP encryption key.
In actuality, the concept behind this method is very simple but still, it isn’t something that you could easily teach to others especially if they do not fully understand the basics of data encryption and decryption. This is one of the reasons why the program provides a detailed tutorial as to how it should be used and if ever you encounter some difficulties, you can always refer to its Help File. It’s quite good to see that the developer of this program did make some extra effort to teach its users the proper way of sending and decrypting email messages. This feature is very useful especially for those who are planning to make use of InstantCrypt for the very first time.
Basically, the entire process consists of four steps. The first step is to create your own encryption key. Without this key, other users won’t be able to send you their encrypted messages. Of course, for every encryption key that you create, you also need to provide a secure passphrase or password. When it comes to using this program, you need to consider the following pointers:
- Your contact needs your encryption key so that he or she will be able to send you an encrypted email message
- You need your contact’s encryption key so that you will be able to send him/her an encrypted email message
On the other hand, decrypting the email messages that you have received is also very easy. Just create a new mail message, copy and paste the encrypted text that you’ve received on the “Encrypted Message” box, press the “decrypt” button then enter the required passphrase. After that, you will be able to see decrypted file in the “Message Text” area.
So far, I did not experience any issues while using this program. It’s just that when it comes to sending emails, you can only send one email at a time. You cannot send your messages to multiple recipients and if you are not used to using such types of programs, you might find it difficult to send and receive mails even if you have already gone through the basic steps in the welcome tutorial.
Conclusion and Download Link
InstantCrypt is a reliable email encryption program and it is definitely ideal for users who want to send and receive encrypted emails. The best part is InstantCrypt works with pretty much all email services, whether that be web mail like Gmail, Yahoo, Outlook.com, or desktop mail using Outlook. It is a very stable software that you can use on a daily basis. If you want to protect your privacy and send/receive encrypted emails, I highly recommend InstantCrypt. However, if you don’t have enough knowledge about this type of data encryption method, I suggest that you read the Help file first so that you will know how to properly use this program.
Price: Free
Version reviewed: 2.3.1
Supported OS: Windows XP, Vista, Windows 7, Windows 8
Download size: 6.9MB for the installer file, 2.7MB for the portable Zip file
VirusTotal malware scan results: 0/44
Is it portable? Yes

 Email article
Email article