 If you’re a true security nut, you’ve probably heard of TrueCrypt. It’s that free hard drive encryption program that’s unfortunately quite complicated. If you’re looking for a trouble-free way to encrypt your hard drives, DiskCryptor might be the program for you.
If you’re a true security nut, you’ve probably heard of TrueCrypt. It’s that free hard drive encryption program that’s unfortunately quite complicated. If you’re looking for a trouble-free way to encrypt your hard drives, DiskCryptor might be the program for you.
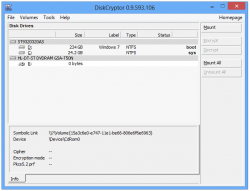
DiskCryptor allows you to encrypt your hard drive, thumb drive, or even optical drive with various forms of encryption. By default, it uses AES encryption, but can also be set to Twofish, Serpent, or AES-Twofish.
To encrypt a drive, just select it in the left pane and click the Encrypt button in the right. It might take a few minutes, but eventually the selected partition will be nicely encrypted for easy security.
Overall, DiskCryptor is a nice disk encryption program. It’d be nice if it supported the creation of virtual disks like TrueCrypt did, but the lack of this feature is one of the things that keeps it from being so complicated.
Price: Free!
Version discovered: v0.9.593.106
Supported OS: Windows
Download size: 701KB
VirusTotal malware scan results: 0/41
Portability: Requires installation
[via AddictiveTips]

 Email article
Email article