In today’s computerized, networked world, it is very important that we protect our private and sensitive data. One way to protect your data is to use steganography; another way is to use encryption. We have already covered the best free steganography program for Windows. Now, in this article, we will explore the best free file-level, folder-level, and drive-level encryption programs for Windows.
This review is part of our Best Free Windows Software section. Check out more articles on the best free Windows programs from here.
BEFORE WE BEGIN
There is one thing I would like to clarify before we begin.
When it comes to encryption, there are two distinct types of encryption: file-level encryption and folder-level/drive-level encryption. File-level encryption is encrypting individual files while folder-level/drive-level encryption is having an encrypted container that holds as many files as you want. Both types can be used interchangeably but file-level encryption is primarily designed for people who want to encrypt a few individual files while folder-level/drive-level encryption is designed for people that want to encrypt either a bunch of files, whole folders, entire partitions (including your system/Windows partition), or whole drives (including internal hard drives, external hard drives, USB flash drives, CDs/DVDs, etc.). This review looks at both best free file-level encryption program and best free folder-level/drive-level encryption program.
That said, let’s begin…
File-Level Encryption Programs
Table of Contents [AxCrypt vs EncryptOnClick vs Cryptographic Encryptor vs 7-Zip vs GoAnywhere OpenPGP Studio]
- Best Free File-Level Encryption Program
- Runner Up
- Honorable Mention 1
- Honorable Mention 2
- Honorable Mention 3
- Other Alternatives
Best Free File-Level Encryption Program
 Program Name: AxCrypt
Program Name: AxCrypt
Developer: Axantum
Download Size: 3.2 MB (installer), 461 KB (portable)
Version Reviewed: 1.7.2976.0
Supported OS: Windows 2003/XP/Vista/2008/7
Pros
- Allows users to encrypt any file and file type using a user-selected password; encrypted files can only be decrypted/accessed with that password
- Securely encrypts files using AES 128-bit encryption
- Note: I know some people may be thinking “but isn’t AES 256-bit better”. Yes, AES 256-bit is technically better but AES 128-bit is secure and provides more security than the average Joe needs.
- Allows users to pick if they want to encrypt the target file or create a copy of the target file and encrypt the copy
- Can easily batch encrypt (or decrypt) multiple files at the same time (each file is encrypted using the same password but is encrypted separately)
- Allows users to create self-extracting, standalone encrypted EXE files which can be decrypted without the need to install AxCrypt
- Encrypted files can either be permanently decrypted or temporarily decrypted (which automatically re-encrypts the target file after you have closed it)
- Allows users to optionally use key files for more secure encryption
- Has a built-in secure file shredder that uses one pass PRN overwrite to securely delete files; this shredder is used automatically by AxCrypt in situations that it needs to shred files (such as in the case of temporary decryption) and you have the ability to manually run it, too
- Automatically compresses encrypted files using Zlib, ensuring encrypted files are as small in size as possible
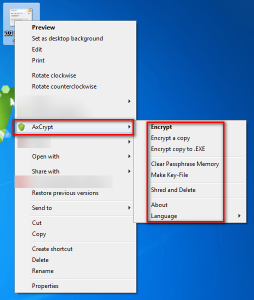
- Is extremely easy-to-use; adds an AxCrypt entry in the right-click context menu from which you can easily encrypt/decrypt files
- Has a portable version which does not require administrator access to run
- Open-source
Cons
- Installer version comes bundled with crapware; be sure to uncheck the relevant boxes and/or decline installation of crapware when you install AxCrypt
- Portable version of AxCrypt (AxCrypt2Go) doesn’t have all the features of the installed version; with the portable version you can encrypt/decrypt files but nothing more (e.g. you can’t create self-extracting EXEs nor can you temporarily decrypt nor can you encrypt the target file — always a copy of the target file is encrypted)
- Temporary decryption is not available when using self-extracting EXEs
- Installer version of AxCrypt has no main program interface; all features are accessed via the right-click context menu
- There is no ability to automatically update AxCrypt
- Note: Some people may consider it a security measure that an encryption program does not automatically update (because it doesn’t automatically access the Internet). However, there should at least be an option to automatically update for those of us that don’t mind it.
Hasn’t been updated since December 2011, so development may have stalled (although it still works perfectly)Note: AxCrypt is open-source so even if the original developer stops developing it, it can easily be picked up by other developers- UPDATE: It looks like AxCrypt was last updated in Nov 2012 but that build is not available on AxCrypt’s Soureforge page
Discussion
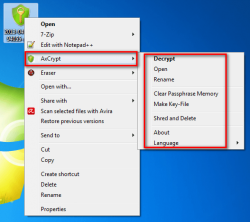 AxCrypt is a file-level encryption program that allows users to easily encrypt/decrypt files from the right-click context menu of Windows. After you install AxCrypt, an “AxCrypt” submenu is added in the right-click context menu of files and folders; from this submenu you can easily access AxCrypt features. In fact, AxCrypt’s installer version has no program interface — it must be used via the right-click context menu. To some not having a main program interface may be annoying but this is actually one of the reasons why I love AxCrypt: it is extremely convenient to be able to encrypt — or decrypt — files by simply right-click them.
AxCrypt is a file-level encryption program that allows users to easily encrypt/decrypt files from the right-click context menu of Windows. After you install AxCrypt, an “AxCrypt” submenu is added in the right-click context menu of files and folders; from this submenu you can easily access AxCrypt features. In fact, AxCrypt’s installer version has no program interface — it must be used via the right-click context menu. To some not having a main program interface may be annoying but this is actually one of the reasons why I love AxCrypt: it is extremely convenient to be able to encrypt — or decrypt — files by simply right-click them.
To say AxCrypt allows you to securely encrypt files would be to state the obvious, so I won’t say it. Rather, I’d like to point out other features that make AxCrypt notable: its ability to create self-extracting encrypted EXE files, the ability to temporarily decrypt a file, and the option it gives users to use key files for enhanced protection. On top of that, AxCrypt has a portable version (dubbed AxCrypt2Go) which you can use if you don’t want to install AxCrypt; AxCrypt2Go doesn’t require administrator access so you can put AxCrypt2Go on a USB flash drive and take it with you to use on any computer you see fit. However, AxCrypt2Go is limited to only encrypting/decrypting files and doesn’t have all the same features as the installed version of AxCrypt, but it is still very useful for those that need encryption on the go. (Note: Axcrypy2Go does not work via the right-click context menu; it has a main program interface.)
Really the only main downside to AxCrypt is the fact that its installer version comes bundled with crapware. While installing AxCrypt you will be prompted to install bundled crapware vis-a-vis OpenCandy. You can easily opt out of this crapware by unchecking the relevant textboxes and/or declining the offer and it is understandable that a developer wants to monetize his freeware, but it is still annoying.
Overall, AxCrypt is, without a doubt, the best file-level encryption program I’ve ever had the pleasure of using. It is extremely easy-to-use, feature-filled, and secure and the downsides are few. Really, what more could you ask? If you need a file-level encryption program, AxCrypt is the way to go — look no further.
Runner Up
 Program Name: EncryptOnClick
Program Name: EncryptOnClick
Developer: 2BrightSparks
Download Size: 1.5 MB
Version Reviewed: 1.4.1.2
Supported OS: Windows XP/2003/Vista/Win7/Win8
Discussion
EncryptOnClick is a very simple program that allows you to easily encrypt/decrypt files using AES 256-bit encryption; batch processing is supported, so you can encrypt individual files at a time or multiple files a time with the option to easily encrypt all the files inside a folder. Unlike AxCrypt which works from the right-click context menu, EncryptOnClick has a main program interface from which you encrypt/decrypt files. In fact, EncryptOnClick doesn’t even add any entries to the right-click context menu.
EncryptOnClick doesn’t some of the features of AxCrypt, most notably lacking the ability to create self-extracting EXEs and to use key files. However, EncryptOnClick differentiates itself in one way: non-proprietary method of encryption.
You see EncryptOnClick encrypts files using AES 256-bits, yes, but it encrypts files in such as way that any archive program that supports encrypted archives can decrypt encrypted files (as long as the proper password is inputted, of course). This means you can decrypt files encrypted by EncrypOnClick using 7-Zip, WinZip, or a host of other archiver programs that support encrypted archives. Take note files encrypted with EncryptOnClick are of the .EOC format (not .ZIP) so you must manually point your archiver to extract the contents of an encrypted file (e.g. if you have 7-zip, right-click -> 7-Zip -> Extract) in order to decrypt.
Also, it should be noted EncryptOnClick can be made portable. It has no separate portable version, but after you install it you can copy + paste three files (EncryptOnClick.exe, EncryptOnClick.exe.manifest, and XceedZip.dll) onto any USB flash drive or other portable media and use EncryptOnClick on any computer without installation; no admin access is needed.
Overall, EncryptOnClick is a good, easy-to-use file-level encryption program. If you don’t like or don’t want AxCrypt, EncryptOnClick is an excellent alternative.
Honorable Mention 1
 Program Name: Cryptographic Encryptor
Program Name: Cryptographic Encryptor
Note: VSEncryptor is another name for Cryptographic Encryptor
Developer: Loxibit
Download Size: 2.3-3.6 MB
Version Reviewed: 2.1.3.495
Supported OS: Windows XP/Vista/Win7/Win8
Discussion
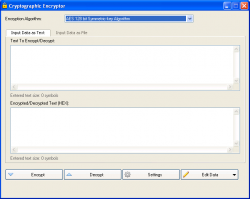
Cryptographic Encryptor is an encryption program that allows users to perform two types of encryption: text encryption and file encryption. For both text and file encryption you are allowed to pick what type of encryption algorithm to use: AES-128, AES-192, AES-256, RC2, RC4, DES, Triple DES, Blowfish, Twofish, Serpent, Camellia, Skipjack, CAST-256, MARS, RC5, RC6, IDEA, SEED, SHACAL-2, XTEA, or GOST.
Cryptographic Encryptor has a main program interface from which you do all the encryption/decryption but it also adds an entry in the right-click context menu for easy encryption of a file, which launches the main program interface when used. And Cryptographic Encryptor comes in both installer and portable versions, and the portable version has all the features of the installer features — including the right-click context menu entry.
One of my most favorite features of Cryptographic Encryptor is the fact that you can control if you want to modify the file extension of an encrypted program or not. For example, by default Cryptographic Encryptor adds a ‘.encrypted’ extension to the end of encrypted files (e.g. test.txt.encrypted). You have the ability to change this extension to whatever you want (e.g. test.txt.dotTech) or remove it all together.
The biggest downside to Cryptographic Encryptor is the fact that it can only encrypt/decrypt one file at a time; batch encryption/decryption is not supported, which is a huge con and makes the program annoying to use if you ever want to encrypt/decrypt more than one file at a time.
Like all programs, Cryptographic Encryptor has its high points and its low points. Overall, however, Cryptographic Encryptor is a viable choice for encryption program.
Honorable Mention 2
 Program Name: 7-Zip
Program Name: 7-Zip
Developer: Igor Pavlov
Download Size: 1.5 MB
Version Reviewed: 9.20
Supported OS: Windows NT/98/Me/2000/XP/2003/Vista/Server 2008/7
Discussion
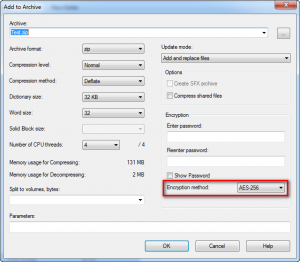
7-Zip is not an encryption program. It is an archive utility, a program that creates and extracts archives (ZIP, 7z, RAR, etc.). In fact, 7-Zip is the best free archive program for Windows. However, even though 7-Zip is not an encryption program per se, it has the ability to create encrypted ZIP and 7z archives (using AES 256-bit). So, essentially, you can use 7-Zip to encrypt your files by simply creating a password-protected and encrypted ZIP or 7z archive.
All encrypted archives created by 7-Zip can be extracted using any file archiver that supports encrypted ZIP/7z archives — you don’t necessarily need 7-Zip to extract an encrypted archive.
Because 7-Zip is not an encryption program per se, it isn’t as user-friendly as AxCrypt. For example, even though you can extract an encrypted ZIP or 7z archive using any of many different archiver programs, you still need some archiver program — it isn’t like a standalone self-extracting EXE that AxCrypt can create, the one that requires nothing but a double-click to decrypt. For example, there are no temporarily decrypts with 7-Zip, no ability to use key files, and it takes a few more clicks to encrypt something with 7-Zip than with AxCrypt. However, even with all those caveats, 7-Zip can easily be used to securely encrypt files when you don’t have or don’t want to install AxCrypt.
UPDATE: You can create self-extracting encrypted EXE files with 7-Zip by using the “Create SFX Archive” option.
(NOTE: Technically speaking, since 7-Zip creates encrypted archives and doesn’t encrypt files themselves, 7-Zip is not a file-level archiving program in the purest definition. In other words, 7-Zip does not encrypt individual files but puts all files inside on encrypted archive. However, 7-Zip is best used for encrypting a handful of files and it isn’t a good option to encrypt a whole drive or large folders, which is why we are featuring it in the file-level section.)
Honorable Mention 3
 Program Name: GoAnywhere OpenPGP Studio
Program Name: GoAnywhere OpenPGP Studio
Developer: Linoma Software
Download Size: 35.8 MB
Version Reviewed: 1.0.1
Supported OS: Windows XP/2003/Vista/2008/Win7/Win8
Discussion
When it comes to encryption, there are two types: symmetric encryption and asymmetric encryption. Symmetric encryption is when you must decrypt a file with the same password used to encrypt it. Symmetric encryption is very secure but a problem arises when sharing encrypted files with others; you need to somehow tell the other party the password required to decrypt the encrypted file without that password being intercepted by a third-party. Asymmetric encryption solves this issue by using a public key-private key architecture.
With Asymmetric encryption, each party involved in the exchange of an encrypted file has one public key and one private key. (These keys are long and mathematically generated; think of them as passwords, but really long and randomized passwords.) Each party shares their public key is shared with the other party while the private key is kept secret. Files encrypted with the public key can only be decrypted by the private key. So, when you want to share files, you encrypt the file using the public key of the recipient who can then decrypt the file using his/her private key; there is no need to transmit a password like with symmetric encryption.
Both programs we have discussed so far, AxCrypt, EncryptOnClick, Cryptographic Encryptor, and 7-Zip, are symmetric encryption tools. GoAnywhere OpenPGP Studio, on the other hand, is an asymmetric encryption tool.
With GoAnywhere OpenPGP Studio you create public-private-key pairs using DSS or RSA 512, 1024, 2048, or 4096 bits. You can then use those keys to encrypt and decrypt files. The idea here is simple: you share the public key you generated with OpenPGP Studio with everyone whom you routinely exchange files. They, too, must have OpenPGP Studio installed and can import your public key into their program. When they want to send you an encrypted file, they use your public key to encrypt the file, which you can then decrypt using your private key (and associated passphrase — when you setup a public-private-key you must select a passphrase). The process is the same if you want to send an encrypted file to someone else; they give you their public key, you use the public key to encrypt, and they use their private key to decrypt. (Batch processing is supported — you can encrypt/decrypt multiple files at a time.)
OpenPGP Studio also has the ability to attach digital signatures to encrypted files, to help tell the recipient who it is that sent the file.
On the face of it, it seems like a no brainier; with asymmetric encryption there is no worry about trying to figure out how to tell the recipient the password required to decrypt. However, asymmetric encryption is not for everyone.
You should only use asymmetric encryption, and therefore OpenPGP Studio, when you routinely exchange encrypted files with the same person or persons. Why? Because this process requires both parties to not only have OpenPGP Studio installed (or whatever other asymmetric program you want to use) but also to have one public-private-key pair each and share the public keys with each other. In other words, asymmetric encryption is not conducive for general encryption needs for the average Joe — symmetric encryption, a la AxCrypt or EncryptOnClick, works much better for that. Symmetric encryption is designed for use when transmission of encrypted files must take place over the Internet; if you are simply looking to protect stored files, such as on your USB drive, or might share encrypted files with people occasionally then symmetric encryption is must better (and faster).
Other Alternatives
- AES Encrypt
- dsCrypt
- Sophos Encryption
- …and many more
Folder-level/Drive-level Encryption Software
All the following create encrypted “containers” which hold the files you want to protect. As such, you can use any of the following programs to encrypt many files, whole folders, entire partitions (including system/Windows partition), or whole drives (internal drive, external, USB drive, etc). Since an encrypted container is used and files are not encrypted at the individual level, you encrypt using one password and decrypt using the same password — you don’t need to have a separate password for each file.
Table of Contents [TrueCrypt vs SafeHouse Explorer vs DiskCryptor]
- Best Free Folder-level/Drive-level Encryption Program
- Runner Up
- Honorable Mention
- Other Alternatives
Best Free Folder-Level/Drive-Level Encryption Software
 Program Name: TrueCrypt
Program Name: TrueCrypt
Developer: TrueCrypt Foundation
Download Size: 3.3 MB
Version Reviewed: 7.1a
Supported OS: Windows 2000/XP/Vista/Win7
Pros
- Allows users to create three different type of encrypted volumes: encrypted containers that protect any files and folders you put in, encrypted partitions (including the system Windows partition), and encrypted drives (including internal drives, external drives, USB flash drives, CDs/DVDs, etc.)
- You can have as many encrypted volumes as you like
- Encrypted containers, partitions (including operating system partition), and drives can be hidden (aka plausible deniability)
- When encrypting operating system partition, uses pre-boot authentication
- Allows users to pick if they want to use AES 256-bit, Serpent 256-bit, Twofish 256-bit, AES-Twofish, AES-Twofish-Serpent, Serpent-AES, Serpent-Twofish-AES, or Twofish-Serpent encryption
- Allows users to pick if they want to use RIJPEMD-160, SHA-512, or Whirlpool hash algorithm
- Allows users to pick the total size of encrypted container (e.g. 200 MB) and you can put as many files inside the container that fit in the specified size; or you can create a dynamic container which automatically grows in size if the files you have inside surpass the limit you selected
- Users are giving the option of selecting file system (FAT, NTFS, or none) and cluster size for containers
- In addition to traditional passwords, users can optionally use keyfiles
- Files/folders inside encrypted volumes can easily be accessed (opened, edited, deleted, renamed, moved, etc.) by mounting the encrypted volume and accessing it in Windows Explorer like it is a drive or folder (like a disc image)
- Note: You need to dismount volumes after you are done with them to re-encrypt them
- Note: Encrypted volumes can be mounted on any computer that has TrueCrypt installed
- Note: You obviously cannot access encrypted volumes without the associated password (and keyfile, if applicable)
- You can mount encrypted volumes as read-only, if you want
- Encrypted volumes can automatically be dismounted when: user logs off, screen saver is turned off, power saving mode is enabled, and/or no data is read or written to volume for X minutes
- Can automatically mount all device-hosted volumes upon login of Windows
- You can mount (aka view and access) over a dozen encrypted volumes at a time, if you like
- Mounting/dismounting and accessing files inside volumes is seamless and very fast — no need to wait a long time for encryption/decryption to happen, everything is on-the-fly
- Can be made portable
- Is open-source
Cons
- Can be very confusing to use for new users, although there is quite a bit of documentation you can read and once you get the hang of it isn’t that complicated
- You need administrator access to install TrueCrypt. For people with admin access that is no big issue but people without admin access need to have their administrator install TrueCrypt before it can be used. This also means you can only use the portable version of TrueCrypt on computers you have admin access to.
- Note: See SafeHouse Explorer if you want to be able to encrypt/decrypt without requiring administrator access.
- Depending on the size of the container you create or partition/drive you encrypte and the speed of your computer, it can take a while to create a new encrypted volume
- It doesn’t happen too often but it is a known problem that sometimes TrueCrypt volumes can become corrupted and all data within the containers lost
Discussion
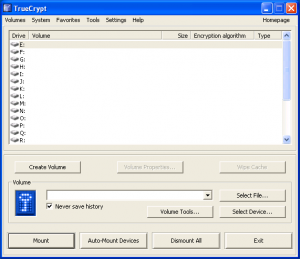
TrueCrypt is the best and most widely respected folder-level/drive-level encryption program.
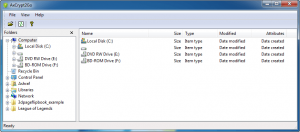
TrueCrypt works by allowing users to create encrypted volumes that are password protected; these volumes can either be encrypted containers that hold any files/folders you put in them, encrypted partitions (including your system/Windows partition), or encrypted hard drives. Once you have an encrypted volume created, all the files/folders inside that volume are protected — no one can access them without your password first.
You put files/folders inside an encrypted volume by mounting it from within TrueCrypt, similar to how you mount an ISO file. Once mounted, a TrueCrypt volume appears in My Computer as if it were a normal drive and you interact with the volume just like a normal drive; to put files inside the volume, simply copy (or cut) files/folders from their original location and paste them inside the TrueCrypt volume. Accessing the files is done the same way; mount the volume within TrueCrypt and you can open/edit/delete/rename/move/copy/etc. all files and folders inside the volume just like you would do with a normal folder.
Once you are done accessing the files/folders inside a TrueCrypt volume, simply dismount it and the volume is re-encrypted automatically.
You can take your TrueCrypt volumes with you wherever you go and mount/dismount them on any computer that has TrueCrypt installed. Furthermore, since TrueCrypt itself can be made portable, you can even take TrueCrypt with you on-the-go, nullifying the need for TrueCrypt to be installed on any computer you want to access your encrypted files on. Do take note, however, TrueCrypt requires administrator access so you won’t be able to use TrueCrypt (i.e. you won’t be able to mount or dismount volumes) on computers that you don’t have admin access on.
The best aspect of TrueCrypt isn’t necessarily its ability to create encrypted volumes but rather its features that go beyond simple folder-level/drive-level encryption. More specifically, TrueCrypt’s ability to create hidden volumes and its ability to encrypt whole system/Windows partitions and use pre-boot authentication makes TrueCrypt stand out above the crowd. Plus its built-in features which help ensure your volumes are automatically dismounted after you are done using them are very useful.
Overall, there is no doubt in my mind that TrueCrypt is the best free folder-level/drive-level encryption program. If you need to encrypt a lot of files, entire folders, whole partitions (including your system/Windows partition), or entire hard drives, TrueCrypt is the way to go.
Runner Up
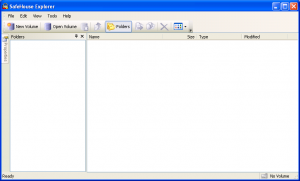 Program Name: SafeHouse Explorer
Program Name: SafeHouse Explorer
Developer: PC Dynamics
Download Size: 3.4 MB
Version Reviewed: 3.01
Supported OS: Windows XP/Vista/Win7/Win8
Discussion
Like TrueCrypt, SafeHouse Explorer allows you to create encrypted volumes (using Twofish 256-bit) and store files/folders you want to keep safe inside those volumes. No one can access your files/folders without your password, and you must mount volumes to access the files/folders inside. Once mounted, you can access files/folders from Windows Explorer like a real folder/drive or via SafeHouse Explorer’s main program interface.
The big difference between TrueCrypt and SafeHouse Explorer is the trade-off between ease-of-use and features. All the awesome features of TrueCrypt, such as encrypting whole partitions/hard drives, creating hidden volumes and automatic dismount, are not in SafeHouse Explorer. Indeed, compared to TrueCrypt, SafeHouse Explorer is a simple encryption program that allows you to create encrypted volumes and mount/unmount the volumes (it cannot encrypt whole partitions or drives). However, the lack of features makes SafeHouse Explorer significantly easier to use than TrueCrypt; there aren’t so many options that can confuse new users. So it is up to you to decide what you value more: better security or lack of a learning curve? If you want better security, TrueCrypt is the clear winner. If you want an ease-to-use program with a small learning curve, then SafeHouse Explorer is the obvious pick.
That said, there is one important feature of SafeHouse Explorer I want to point out. As already mentioned, TrueCrypt can be made portable but you need administrator access on computers to run it. SafeHouse Explorer can also be made portable but it has two different ways of being portable. You can download a fully portable version of the program or you can convert individual encrypted volumes into standalone, self-decrypting EXEs. In other words, you can either use SafeHouse Explorer’s portable version or you can make the encrypted volumes you created with SafeHouse Explorer portable. Once you create a standalone EXE out of an encrypted volume, you can open/decrypt that volume and access files/folders on any computer without the need to install SafeHouse Explorer… and you don’t need administrator access. These standalone EXEs allow you to open files, delete files, edit files, rename files, move files, add files, remove files, etc.
Every encrypted volume you create with SafeHouse Explorer can be turned into a standalone EXE which you can take with you and access on-the-go. Do take note, however, that SafeHouse Explorer creates a standalone EXE copy of your encrypted volume — it doesn’t convert the volume itself, so you still have the encrypted volume leftover which you may or may not want to delete afterwards.
Overall, SafeHouse Explorer is a simple encryption program compared to TrueCrypt but it offers distinct advantages that cannot be overlooked. Which program you use depends on what you want and desire. Both are excellent.
Honorable Mention 1
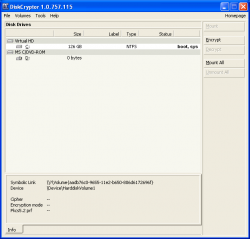 Program Name: DiskCryptor
Program Name: DiskCryptor
Developer: ReactOS Software
Download Size: 980 KB
Version Reviewed: 1.0.757.115
Supported OS: Windows XP/2003/Vista/2008/Win7
Discussion
DiskCryptor is an open-source encryption program specifically designed to allow you to encrypt whole partitions, including system partition thanks to pre-boot authentication, entire drives (including internal, external, and USB flash), and CDs/DVDs.
Like TrueCrypt, DiskCryptor creates encrypted volumes you must mount/unmount and allows users to pick from AES, Serpent, Twofish encryption or a mix thereof. Unlike TrueCypt, DiskCryptor cannot create hidden encrypted partitions/drives and cannot create regular encrypted containers just for files/folders — DiskCryptor is only for those that want to encrypt whole partitions/drives.
According to the developer of DiskCryptor, it is better for encrypting partitions/hard drives than TrueCrypt because DiskCryptor has been specifically designed to work with existing data. How is this? Honestly, I have no clue — I’m not a programmer and it is worth mentioning DiskCryptor actually started off as a fork of TrueCrypt that specialized in partition/drive encryption (although it has since become its own program) However, I can tell you this. DiskCryptor is easier to use than TrueCrypt; new users will find it is a lot easier to encrypt your partitions/drives with DiskCryptor than it is with TrueCrypt. So, based off that, if you want to encrypt whole partitions/drives, DiskCryptor is a worthy competitor.
Other Alternatives
- Rohos Mini USB
- Kryptel
- Cypherix LE
- CompuSec
- FreeOTFE
- …and many more

 Email article
Email article