 The traditional way to fight malware is to use an anti-virus (or anti-malware, if you prefer to call it that). A newer way to protect against malware that has emerged in the last decade or so is using a sandbox — isolating attack vectors (e.g. your browser) so even if you are infected by downloading a malicious file or visiting a malicious website, that infection cannot spread to the rest of your computer. SecuBrowser is a new sandboxing program that aims to help you sandbox your browser and protect you. Let’s see if it does what it claims.
The traditional way to fight malware is to use an anti-virus (or anti-malware, if you prefer to call it that). A newer way to protect against malware that has emerged in the last decade or so is using a sandbox — isolating attack vectors (e.g. your browser) so even if you are infected by downloading a malicious file or visiting a malicious website, that infection cannot spread to the rest of your computer. SecuBrowser is a new sandboxing program that aims to help you sandbox your browser and protect you. Let’s see if it does what it claims.
What is it and what does it do
Main Functionality
SecuBrowser sandboxes your browser with the aim to protect you from malicious malware on the Internet.
Pros
- Works with Internet Explorer and Firefox
- Makes it easy to run your default browser in sandbox mode (as long as it is IE or FF) — simply double-click the SecuBrowser shortcut placed on your desktop
- Won’t conflict with your anti-virus/anti-malware
Cons
- Is a very poor sandbox
- Only works for Internet Explorer and Firefox; Chrome, Opera, and other browsers are not supported
- Does not yet support Windows 8, although developer says Windows 8 will be supported soon
- Makes it difficult if you want to run your non-default browser in sandbox mode; you have to copy the shortcut and modify it to point at Firefox or Internet Explorer (whichever one is not your default)
- Does not work with the sandbox Adobe has put into Reader 11 and higher, so defaults to Adobe’s sandbox when Adobe Reader is run. We all know Adobe Reader’s sandbox has been bypassed before, so… yeah…
- Why must the developer use an icon for SecuBrowser that very closely resembles the icon for Sandboxie? Tsk tsk.
Discussion
 While not perfect, sandboxing is an excellent way to protect yourself from malware. So when I came across SecuBrowser, I was very excited. Another sandboxing program can only be a good thing, right? Eh, not so much.
While not perfect, sandboxing is an excellent way to protect yourself from malware. So when I came across SecuBrowser, I was very excited. Another sandboxing program can only be a good thing, right? Eh, not so much.
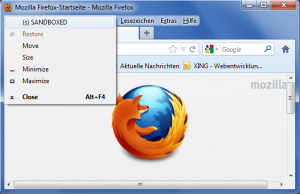
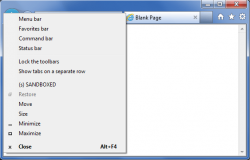
As per my tests, this is how SecuBrowser “sandboxes” your browser. After installed, it places a shortcut on your desktop which you must double-click to run your default browser in sandbox mode. When you do that, all files (including temporary files) generated by that browser session are saved in a C:/sbox/[user name] folder on your hard drive. The idea here is if you come across a malware infested website while surfing the web, the malware will be downloaded to the C:/sbox/[user name] folder and you can easily get rid of the malware by deleting that folder. The only problem? This is an extremely stupid sandboxing method.
SecuBrowser restricts write/modify restrictions for your browser, forcing it to write to C:/sbox/[user name]. Cool, that is good. The issue is SecuBrowser has absolute no control over malware execution once it is downloaded to the C:/sbox/[user name]; if you ever happen to be infected with a drive-by attack on a website, all SecuBrowser will do is ensure all malware related files are downloaded to C:/sbox/[user name] — it won’t actually stop the malware from executing and accessing other parts of your system, nor can it stop a virus from replicating to other files in your system. In other words, it isn’t really a sandbox.
On top of that, SecuBrowser does not have the ability to automatically delete the contents of C:/sbox/[user name] (e.g. like on a reboot or after browser session has ended); you must manually delete that folder every time you want the contents gone, such as if you suspect malware infection. This means if you are infected while in a sandboxed browsing session, the infected malware will sit on your computer in C:/sbox/[user name] until you manually delete the folder. Who is going to remember that they should regularly delete C:/sbox/[user name]? Not very many people, I suspect.
Oh and you haven’t even heard the best part yet.
SecuBrowser restricts all files generated during the browser session to C:/sbox/[user name]… except for files you download yourself. Files or programs that you download yourself are placed in the Downloads folder in My Documents or the Downloads library, depending on what version of Windows you are running. Once downloaded, you can run/open the files/programs as normal, and those files/programs have access to your whole system like normal — SecuBrowser does not restrict the system access downloads have to your computer. So, essentially, if you unknowingly download a program with malware, SecuBrowser will do nothing to protect you except sit there and watch. Again, not a sandbox.
Conclusion and download link
Is this program a joke? Either this was programmed by a kid (which I doubt, since the developer claims to have a wife) or an amateur because, as per my testing, this is not a sandboxing program despite what the developer claims. In fact, I’d say this is a hoax more than anything. (Either that or I completely misunderstood what this program does, which is a possibility.) Based off my experience with this program, I wouldn’t touch SecuBrowser with a ten-foot pole if I were you, at least not in its current form. Rather, if you want a competent sandboxing program, check out Sandboxie. Sandboxie is an excellent sandboxing program that has a feature-limited, but still useable, free version with the full version costing €29.
Price: Free
Version reviewed: 1.0.0.0
Supported OS: Windows XP/Vista/Win7
Download size: 900KB
VirusTotal malware scan results: 0/46
Is it portable? No

 Email article
Email article