Are you aware of the fact that most of the apps and extensions that you use on Chrome require access to your account? As a matter of fact, this is not just limited to your Chrome extensions and apps. The same goes for your web apps. For as long as a web app would ask you to log-in or link your Google account, then you are allowing that app to view or access some parts of your personal account or data. Like, for example, you’re allowing Appbrain or Facebook to access your basic account info.
The thing is some apps will retain that access even if you have already stopped using them. So to be sure, you can opt to manually revoke the app’s access to your account. Speaking of which, here’s how to remove the apps linked to your Google account.
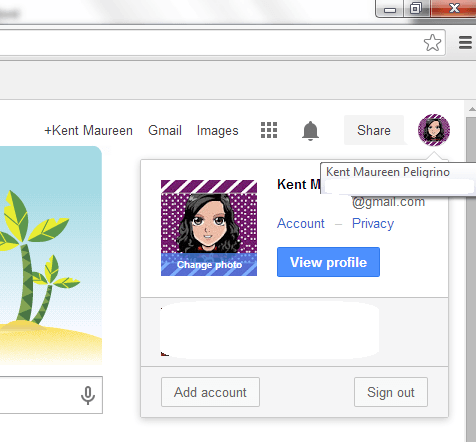
Step 1
Log in to your Google account using your email and password.
Step 2
Once you’re logged in to your Google account, go to your Google or Gmail home page then click your profile photo.
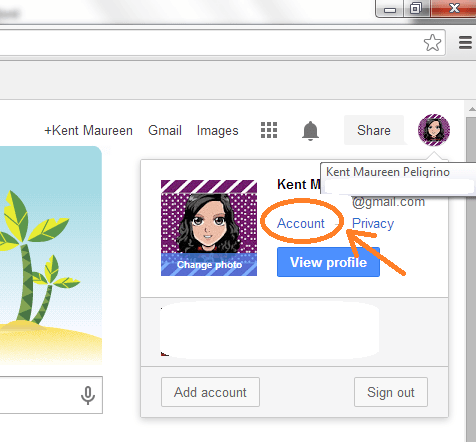
Step 3
A small window will appear and there, you’ll be able to view your profile, change your account privacy or sign out. Just click “Account” to go to your “Personal Info – Account Settings”.
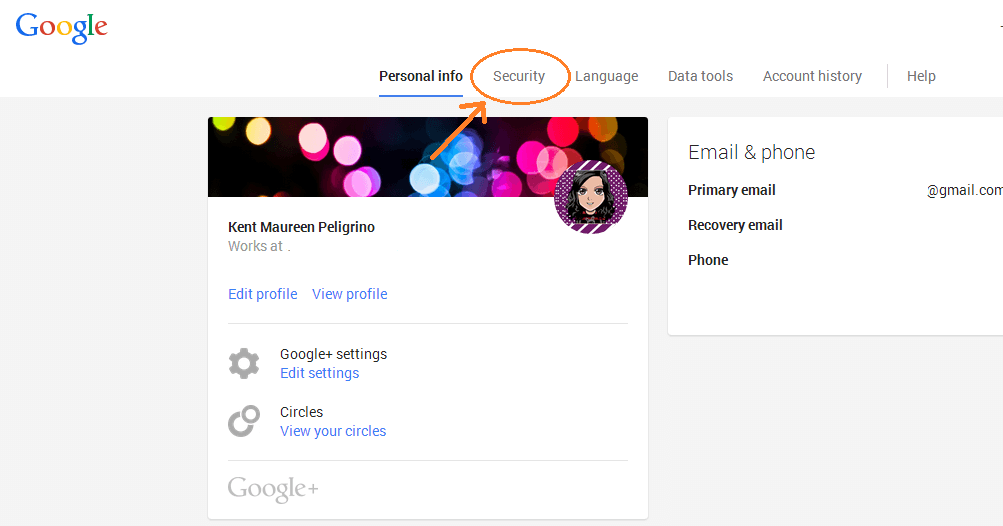
Step 4
On your “Personal Info – Account Settings” page, click the “Security” tab.
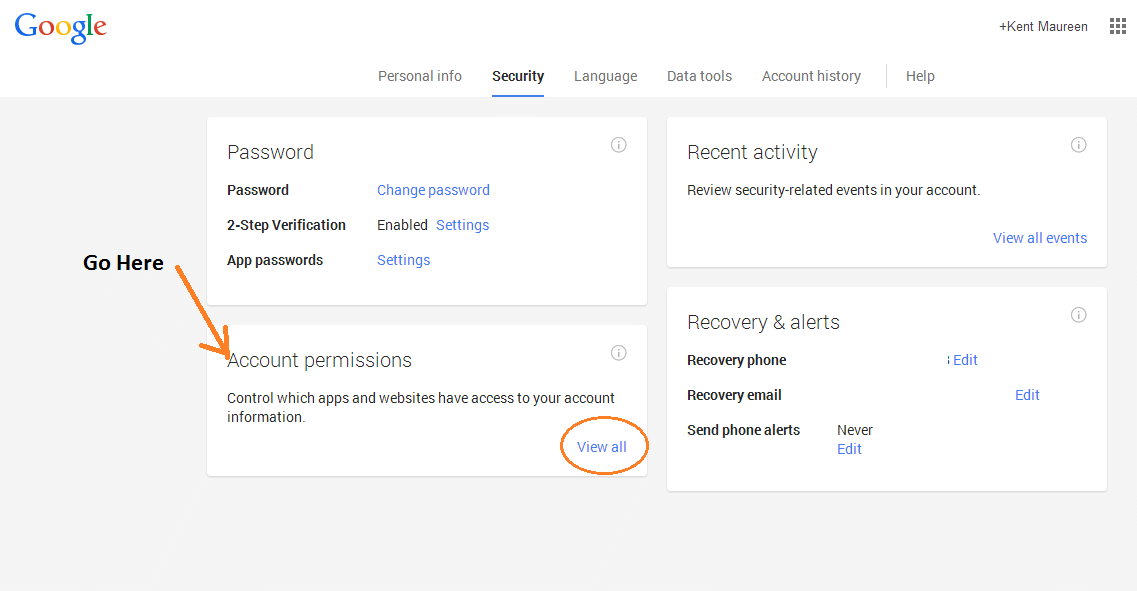
Step 5
Under your “Security” tab, go to the section for “Account Permissions” then click “View All”.
Step 6
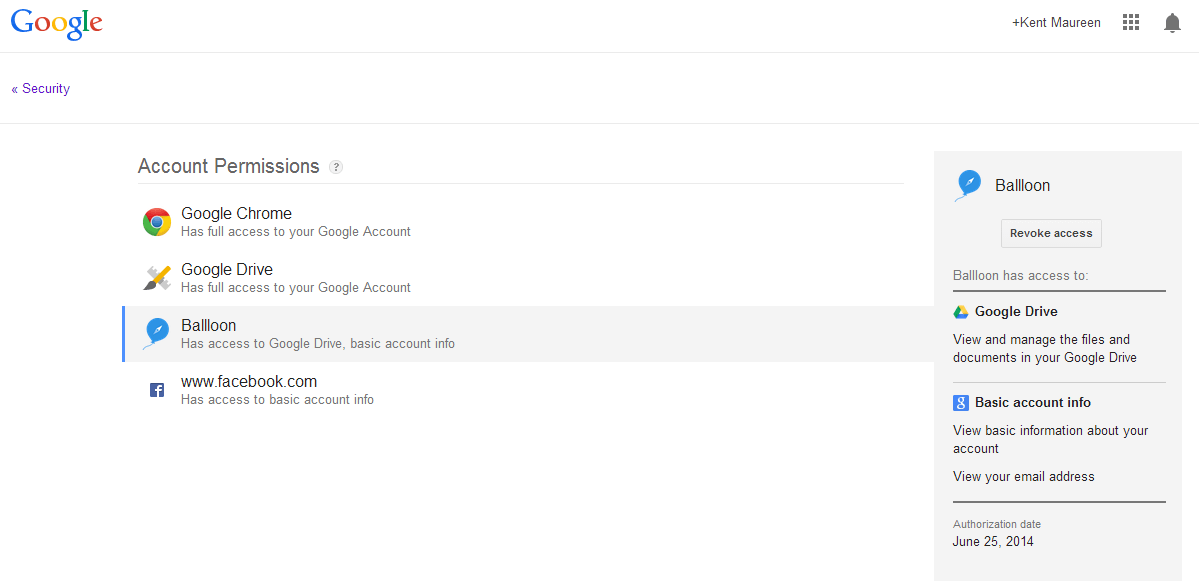
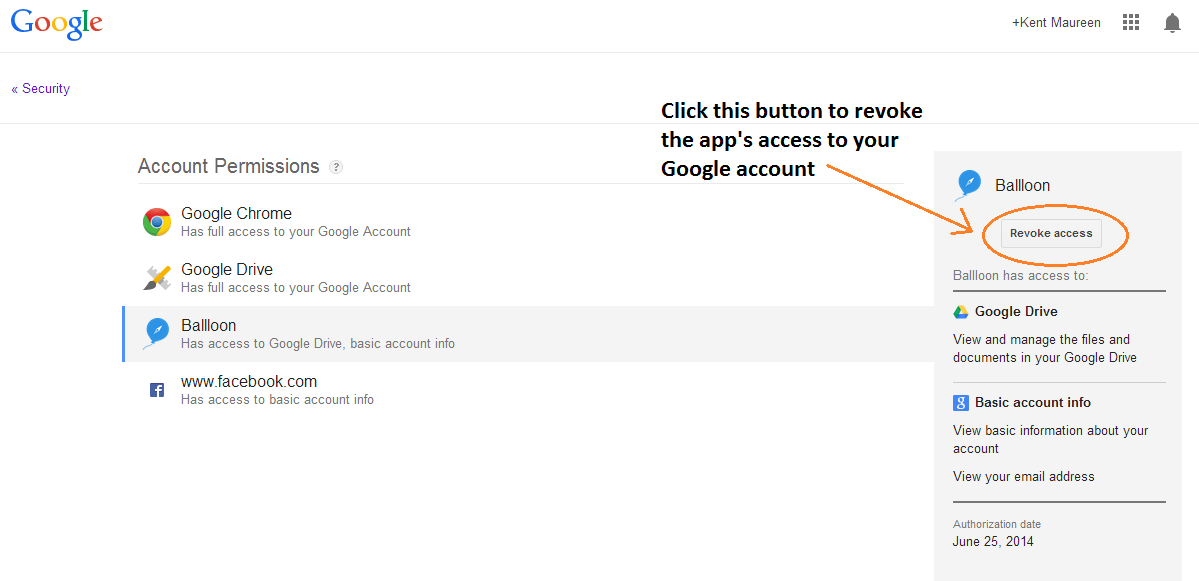
On your “Account Permissions” page, you’ll see the full list of apps and extensions that can freely access your account. Some of these apps may have full account access while there are also those with very limited access. Just click on any app to determine the type of permissions that you’ve granted.
Step 7
To remove an app or extension from your account, just click on it then on its corresponding sidebar menu, just click the button for “Revoke Access”.
Just keep in mind that once you delete the app from your “App Permissions” page, you’ll have to re-authorize it if ever you wish to use it again.
Anyways, this method can be quite useful especially if you want to clean up your Google account. This will also help keep your account safe from privacy breach and other forms of malicious attacks.

 Email article
Email article