File encryption is a tricky business. We all have some files that we would like to keep encrypted so they are kept out the reach of others. Yet, there are so many encryption software out there. Which one should we use? Which ones can we trust? (After all, we don’t want to ensure the security of our files just to anybody.) Which ones will sufficiently help protect our files without giving is a headache? Simply put, AxCrypt and/or TrueCrypt will.
AxCrypt and TrueCrypt are both free, open source encryption tools that have not only been time tested, but are trusted as authorities in the encryption software genre. They use the best techniques when it comes to encryption, so your files are safe. Yet, they are not so overly complicated that you will want to pull your hair our learning how to use them. (Okay, TrueCrypt is a little bit complicated, but spending the time to learn it pays off.)
The reason I mention both AxCrypt and TrueCrypt in this article is because they provide two different types of protection. AxCrypt provides single-file-encryption capabilities. In other words, you will use AxCrypt to encrypt files individually; you can encrypt multiple files at once but each file is encrypted separately so when decrypting you need to decrypt each file (you can decrypt multiple files at once). TrueCrypt, on the other hand, does not provide the encrypt-single-file ability. Rather, TrueCrypt allows you to perform “group” encryption. In other words, TrueCrypt takes multiple files and puts them into an “encrypted container”; each encrypted container can hold as many files as you want, and you can create as many encrypted containers as you want. Decrypting the container gives access to all the files; you don’t need to decrypt each file individually. The differences between AxCrypt and TrueCrypt, then, is AxCrypt is intended for users that need or want to encrypt files individually and TrueCrypt is intended for those that need or want to encrypt a large number of files, such as multiple files together, whole hard drives or partitions, or even portable devices.
To put it in an analogy, think of AxCrypt vs TrueCrypt like this. Lets say you live in an apartment building. One day a crazy rabid, um, donkey escapes from the local zoo. To protect yourselves from this rabid donkey you and everyone in the apartment building have two choices. You can either go inside your individual apartments and lock the door; or you can lock the door to the apartment building. (For the purposes of this analogy lets assume the donkey cannot break down the doors nor can it get in any other way.) Either course of action will result in you all being saved from the donkey. Similarly, AxCrypt – which is analogous to locking each individual apartment door – and TrueCrypt – which is analogous to locking the apartment building door – both provide you with protection; they just go about it in different ways.
[Note: Once you encrypt file with AxCrypt or TrueCrypt, you can put the encrypted files anywhere you want, including on USB flash drives, CDs, DVDs, external hard drives, etc. Both programs can even have modes that allow you to create encrypted files that can be decrypted without having to have AxCrypt or TrueCrypt installed, making them ideal for use of encrypting files you want to take with you on the go. If you need burning software to help you put encrypted files on CD/DVD, see our review on Best Free CD/DVD/Blu-ray Burning Programs for Windows.]
[Note: Portable version of TrueCrypt requires administrator access to run. If you don’t have admin access or foresee using TrueCrypt on a computer without admin access, check out SafeHouse Explorer instead.]
AxCrypt
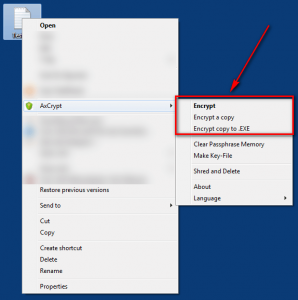
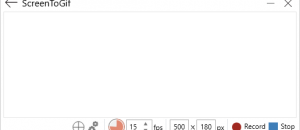
Since AxCrypt is designed for single-file-encryption, it primarily works out of the right-click context menu. When you want to encrypt a file select that file, right-click, go to “AxCrypt” and select how you want to encrypt the file:
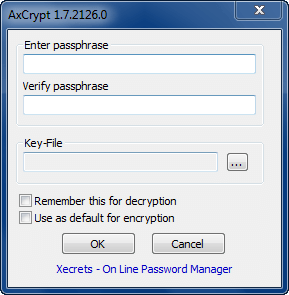
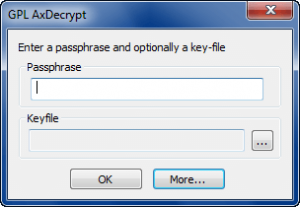
(NOTE: “Key-File” is optional.)
“Encrypt” encrypts the file in question. “Encrypt a copy” makes a copy of the file in question and encrypts that copy (the original file is not encrypted). “Encrypt copy to .EXE” makes a copy of the file in question and makes an encrypted .EXE file of that copy (the original file is not encrypted). The main difference between the “Encrypt”/”Encrypt a copy” and “Encrypt a copy to .EXE” is that “Encrypt”/”Encrypt a copy” create .AXX encrypted files; you need AxCrypt installed to decrypt .AXX files; on the other hand “Encrypt a copy to .EXE” creates .EXE encrypted files; you do not need AxCrypt installed to decrypt .EXE encrypted files. (An encrypted .EXE makes it easier to share the file with other people who may not have AxCrypt installed; keep in mind, though, most e-mail services block the sending of .EXE files as attachments.)
While AxCrypt is an individual-file-encryption tool, AxCrypt still allows you to encrypt multiple files at once. To do this, just select multiple files or select a whole folders (in which case all files in the folders will be encrypted) instead of selecting a single file. If you do select multiple files/folders, keep in mind that the same password will be used to encrypt each individual file.
Once a file has been encrypted by AxCrypt, the file looks something like this:
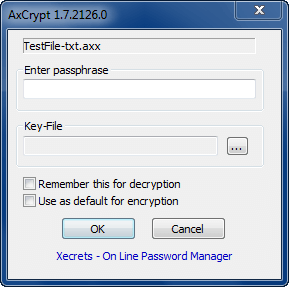
If you want to view an .AXX encrypted file, but not decrypt it, all you need to do double-click on the file to view it; you will be asked to enter the password:
If you enter the right password, you will be able to view the file. Once you are done viewing the file and you close it, the file is automatically re-encrypted.
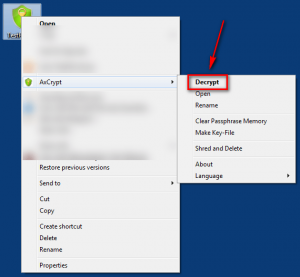
If you want to decrypt an .AXX encrypted file, you can do that too; just right-click it and select “Decrypt”:
You will, of course, be prompted to enter a password and if you get it right the file will be decrypted.
Similar to how you can encrypt multiple files/folders at one time, you can also decrypt multiple files and folders at one time. If the files were encrypted with the same password you will only have to enter the password once and all the files will be decrypted one at a time; if the files were encrypted with different passwords, you will be prompted to enter the password for each file.
Decrypting an .EXE encrypted file, on the hand hand, works a bit differently. For an encrypted .EXE file, you never decrypt the actual encrypted .EXE file. Rather, when you go to decrypt an encrypted .EXE, you create a decrypted copy of the file – the original encrypted .EXE file stays put. To decrypt an .EXE all you need to do is double click on it, enter the password…
…select where you want to save the decrypted file, and viola.
In terms of security, AxCrypt uses 128-bit AES for all encryption, so it is very secure. In addition, it securely shreds and deletes all files after they have encrypted/re-encrypted to make sure no one is able to get their hands on the decrypted files that you were viewing; you also have the ability to manually securely shred and delete files as you can see from the screenshots I presented above. (Admittedly, though, the developer of AxCrypt does not really specify what algorithm is being used to securely shred and delete files.)
Last but not the least, the AxCrypt is also comes in a portable, standalone version (you need to download the installer .EXE and during the installation you will be given the option to extract the portable, standalone version). However, this portable, standalone version is in the Alpha stages, so I would not recommend you use it just yet.
TrueCrypt
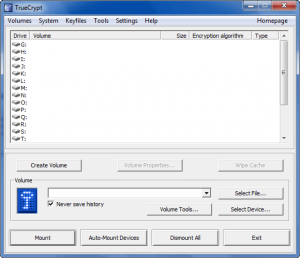
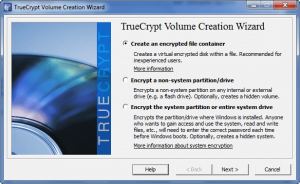
TrueCrypt is a bit more involved and complicated than AxCrypt, but in return it also offers a lot more complexity and flexibility than AxCrypt. Like already mentioned, TrueCrypt works with encrypted containers as opposed to encrypted files. So, to get started with TrueCrypt you must first create a TrueCrypt volume. To do that you need to run TrueCrypt and click “Create Volume” from the main program window. You then need to decide what you want to encrypt:
As you can see from the above screenshot, you have three basic options. You can create a simple encrypted file container, encrypt a whole non-system partition/drive (including portable devices like flash drives), or encrypt the whole system partition/drive. For the purposes of this article, I will only go over the basic features of TrueCrypt (however I will provide a link to an extensive tutorial which you can read to learn about all the nooks and corners of TrueCrypt); the most basic option is the encrypted file container so I will discuss how to create and use that.
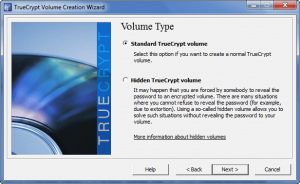
Once you select the “Create an encrypted file container” and click “Next”, you need to select if you want to create a standard TrueCrypt volume, or a hidden one:
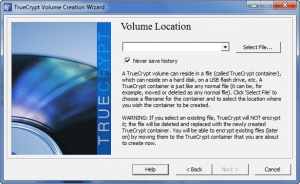
Again I am only discussing the basic features of TrueCrypt so I will talk about the standard volume. After you select the standard volume and click “Next” you are asked to pick where you want to save the volume:
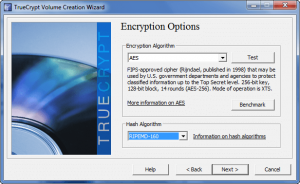
After you have select the location to save the volume and clicked “Next”, you are given the option to select which encryption and hash algorithms you want to use to protect your volume:
For encryption algorithm you can select from AES, Serpent, Twofish, AES-Twofish, AES-Twofish-Serpent, Serpent-AES, Serpent-AES-Twofish, or Twofish-Serpent. For has algorithm you can select from RIPEMD-160, SHA-512, or Whirlpool. For most people the default AES and RIPEMD-160 will do just fine.
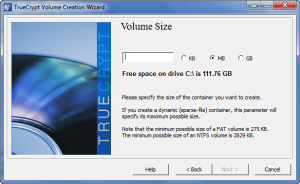
After you have select the algorithms and clicked “Next”, you need to specify the size of the encrypted volume:
The size you enter will determine up to how many files the encrypted volume will be able to hold (i.e. if you set it to one MB, it can hold two 500 KB files, or four 250 KB files, or five 200 KB files, etc.).
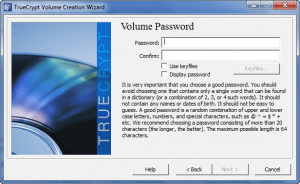
After you have set the size and clicked “Next”, you need to set the password for the volume:
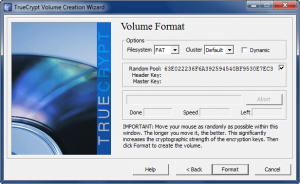
After you have set a password and clicked “Next”, you are ready to actually create the volume:
You have the option to change the filesystem and cluster, but for must of us we should leave it at the default settings. Note that you also have the option to make the volume “dynamic”. A “dynamic” volume is different more a non-dynamic volume in the sense that a non-dynamic volume will always take up the total amount of space on your hard drive that you specified two steps earlier; a dynamic volume, however, will only increase in size as you add more files and when it is totally filled it will take up the total amount of space on your hard drive that you specified two steps earlier. Dynamic sounds better, obviously, but dynamic volume also perform worse and are less secure.
Once you are ready, hit the “Format” button and your encrypted volume will be created (it may take a little bit of time depending on how large you made the volume). Once the volume has been created, you are ready to start placing your files in it.
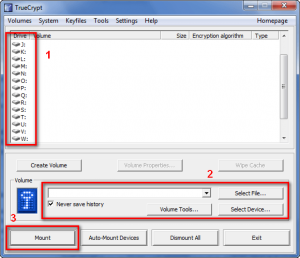
TrueCrypt volumes work similar to how hard drive partitions work; you mount the volumes when you want to access the files in the volume or add/remove files from the volume. When you are done, you unmount the volumes. So, to mount a volume you need to go to TrueCrypt’s main program window, select a drive letter, load the encrypted volume you want to mount, and hit “Mount”:
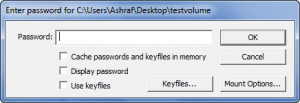
You will be asked for the password for the volume…
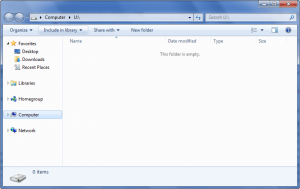
…and after you enter it and hit “OK”, the volume will be decrypted and mounted. Once a volume has been decrypted and mounted, either double-click on the volume from TrueCrypt’s main program window, or go to My Computer and double-click on the volume from there; the volume is then displayed to you:
When the volume opens up, you can can view/edit/add/remove and interact with the volume just like you would a folder on your desktop. In other words, cut and paste files into there if you wish, create new files in it if you wish, edit any existing files if you wish, delete any existing files if you wish, etc. Keep in mind, though, you can only have as many files in the volume as the size of the volume permits. Once you are done interacting with the volume and would like to re-encrypt it, go back to TrueCrypt’s main program window, right-click the volume and select “Dismount” (or hit the “Dismount All” button). Once the volume is dismounted, it is automatically re-encrypted and all the files inside the volume are safe – no one will be able to access the files without first decrypting the volume which they would need your password to do. (TrueCrypt is very secure.)
As I already mentioned, TrueCrypt has many features, many of which I did not discuss in the article. TrueCrypt is truly much too complex to discuss in one simple article. The bright side, though, is that the developer of TrueCrypt has very extensive and useful documentation which users can read if they want to learn all the tricks of TrueCrypt.
Final Words and Download Links
Just like how you can lock both the individual apartment doors and the apartment building door in the analogy I stated at the beginning, you can use both AxCrypt and TrueCrypt together to provide double protection for your files, if you wish. However, even alone each software provides you with ample encryption needs and will help you keep your files for-your-eyes-only. Which one you use totally depends on your needs and desires; both are terrific and well worth the download. Personally I am an AxCrypt user, and prefer its simplicity over TrueCrypt – how about you? Feel free to share in the comments below.
You may download AxCrypt and TrueCrypt from the following links:
AxCrypt
Version reviewed: v1.7.2126.0
Supported OS: Windows 2000/2003/XP/Vista/2008/Win7
Download size: 1.5 MB
TrueCrypt
Version reviewed: v6.3a
Supported OS: Windows 2000/XP/Vista/Win7, Mac OS X, and Linux
Download size for Windows: 3.2 MB
[Direct link to download page]

 Email article
Email article