Software Description
Software Description
The following is a description of Emsisoft Mamutu 3, as per the developer:
Malware protection without signatures?
The Emsisoft Anti-Malware Guard scans all running programs with a signature scanner the same as all other antivirus guards. The scan can only detect the malware if it has the correct signature. Although the Emsisoft Team wish to create signatures for new malware and provide them as fast as possible via the online update, the process of creating a new signature can take a while. During this time you are not protected against new dangers.
This is where our Behavior Blocker comes in. This is a special system which is able to detect and block malware without the need for signatures. The Behavior Blocker is part of Emsisoft Anti-Malware and Mamutu.
Behavior Analysis
Usually, Malware is detected with the help of heuristics. Heuristic scanning analyses the code in a file and decides whether or not it is harmful. The Behavior Blocker works differently, as it watches any active program and stops it if it notices anything suspicious. If a program is trying to change something, you will be told immediately, and given the chance to authorize this change. If the Behavior Blocker pops up a warning when you are not doing anything on your computer, you can be fairly sure that the program is working without your approval.
And this is the way it works.
Malware always wants to achieve a particular result. A virus always infects, a worm always spreads, a trojan always sends files and a dialer always dials. Their methods may differ, but the result is the same.
It is at this point that the Behavior Blocker interrupts the program. It analyses the behavior of all active programs, and alerts you if anything harmful is detected. The program is stopped and cannot continue until you decide whether or not to authorize the behavior.
All this probably sounds too good to be true, and there is one disadvantage: the Behavior Blocker only recognizes behavior, and cannot give you the actual name of the malware in question. In other words, you will know if it’s a worm, but not if it’s the NetSky or Bagle worm. Of course, this doesn’t really matter – the important thing is that you know it’s there, and you can run the appropriate removal program.
What does it detect?
Currently the Emsisoft Behavior Blocker can detect the following malware types:
- Email worms
- Spyware/Adware
- HiJackers
- Backdoor trojans
- Trojan downloader with reverse connection logic
- Dialers
- Keylogger
- Rootkits
- Viruses
In addition, the Behavior Blocker can monitor and stop any of the following actions:
- Installation of new drivers and services
- Any kind of process manipulation like DLL-injection, code-injection, patching, termination, etc.
- Installation of new BHOs (Browser Helper Objects)
- Changes to your Internet Explorer configuration
- Hidden installations of software
- Changes to your Hosts file (redirects domains)
- Installations of debuggers on the system
dotTech Advice
I don’t have a suitable setup to test a security software like Mamutu 3 (i.e. I don’t have a malware invested test machine I can use it on to see how well it works). Plus I’m not a personal user of Emsisoft Mamutu 3 so I can’t tell you my experience with it either. However, from what I hear, Emsisoft Mamutu 3 is very good.
You see Mamutu 3 is a special type of anti-malware program. It is a behavior blocker. Instead of relying on signatures to detect malware, Mamutu analyzes the behavior of files to determine if they are malicious or not — just like the now-defunct but still freeware ThreatFire (Threatfire can still be downloaded but it hasn’t been updated in over two years, so it isn’t very safe to use). The attraction to behavior blockers are a) They tend to find malware missed by signature-dependent security software and B) They can typically be run alongside traditional signature-dependent security software without conflicts. Now I say “typically” because more and more traditional signature-dependent security software are including behavior blockers, so if you already have a security solution that has a behavior blocker, then Mamutu will almost certainly conflict with it. And just because there are no conflicts between Mamutu and your other security software does not mean running Mamutu on top of what you have already won’t have a negative effect on the speed of your computer. You won’t have “conflicts” but it is only logical the CPU usage by Mamutu will have a negative effect on the speed of your computer because without Mamutu that CPU usage could be utilized other places. Really the only way to find out if Mamutu will slow down your computer is trying to run it alongside what you have already for a day or two.
That said, the big question is “Should I get Mamutu?” Well that really depends on your habits. If you regularly visit questionable websites and download questionable files, then Mamutu would be helpful assuming you don’t have a behavior blocker already. If you don’t regularly visit questionable websites and are not a big downloader, then having a behavior blocker on top of your existing security solutions is probably overkill and waste of computer resources. (Note: Mamutu should be used as a compliment to your main, signature-based security solution — Mamutu shouldn’t be run on its own.)
Freebie Details
Emsisoft Mamutu 35 is being given away in a promotion by the DownloadCrew. The promotion is live until Friday 24 February 2012 23:59 Central European Time; there is not information on if you can install/reinstall after this date. Also, note this promotion is for a one year license of Emsisoft Mamutu 3. After the one year either you need to buy Emsisoft Mamutu 3 or stop using the program.
To get Emsisoft Mamutu 3, do the following:
Version being given out for free: v3.0.0.20
Free updates: Yes, but for one year only
Free technical support: I believe, yes
Supported OS: Windows XP (32-bit only), Vista (32-bit and 64-bit), Win7 (32-bit and 64-bit)
Download size: 4.8 MB
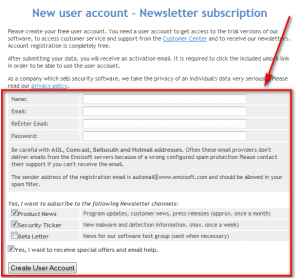
- First thing you need is an account with Emsisoft. (If you already have an account with Emsisoft, skip to the next bullet point in this guide.) Creating an account with Emsisoft is completely free and only takes a few minutes. To create an account with Emsisoft, visit the registration page, fill out the form, and hit Create User Account:
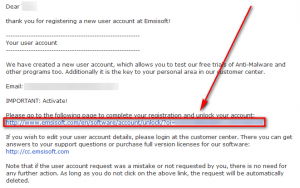
Now check the inbox of the email address you registered with. Look for an e-mail from Emsisoft with subject of Your user account information – Requires verification. In that e-mail there is a link you must follow:
Click on the link or copy + paste it in your browser. Close the page that loads.
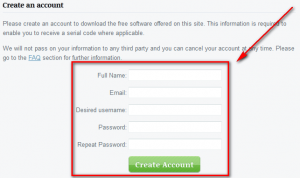
- Next you to have an account with DownloadCrew. Registering with DownloadCrew is completely free and only takes a few minutes. If you already have an account with them, skip to the next bullet point below. If you don’t have an account with them, visit the registration page and register:
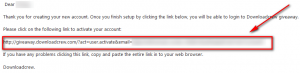
Now check the inbox of the e-mail address you registered with. Look for an e-mail from noreply@giveaway.downloadcrew.com with subject of giveaway.downloadcrew.com – New Account. In the e-mail is a link you need to follow:
Click on the link or copy + paste it in your browser. Once the page loads your account has been confirmed and you can use it.
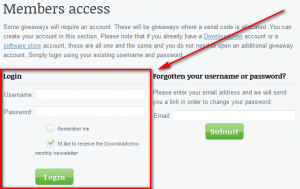
- If you are not already logged in (you may already be logged in if you just created a new account) visit the login page and log into your DownloadCrew account:
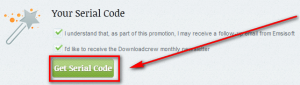
- Visit the promotion page and scroll down about half way and click on the Get Serial Code button:
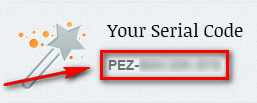
- Copy the serial code that appears:
- Scroll up and click the Download button to begin downloading Emsisoft Mamutu 3:
- After the download finishes, install Emsisoft Mamutu 3.
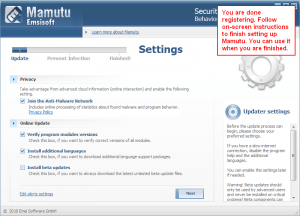
- After installation has finished, run Emsisoft Mamutu 3 and register it with the serial code you were given earlier. If you are confused on how to do that, these screenshots show you — follow the red boxes, arrows, and text:
- Enjoy!
If you have trouble getting Emsisoft Mamutu 3 for free, post below and other dotTechies or I will try to help.
[Thanks PC basics!]

 Email article
Email article