Internet users getting attacked through security flaws or loopholes in one of the most important plug-ins as far as the web browser o f a common user is concerned, Flash, has not been an uncommon situation till now. There have been various discussions and specific criticism on the degree of flaws of the plug-in, which has plenty of flaws which allow remote attackers to inject harmful code into the host computer.
f a common user is concerned, Flash, has not been an uncommon situation till now. There have been various discussions and specific criticism on the degree of flaws of the plug-in, which has plenty of flaws which allow remote attackers to inject harmful code into the host computer.
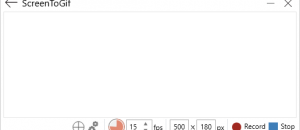
The recent update for Flash player (Flash Player 11.3) brings in not just some minor patches, but also, ‘Flash Player Protected Mode’ for Firefox running on Windows Vista and Windows 7. Firefox already has a layer of protection, which isolates the browser plug-ins by running them as a separate process. Adobe added to this, yet another layer of security by further breaking down the plug-in two distinct processes.
Sandbox, as defined by Wikipedia:
A sandbox is a security mechanism for separating running programs. It is often used to execute untested code, or untrusted programs from unverified third-parties, suppliers, untrusted users and untrusted websites. The sandbox typically provides a tightly-controlled set of resources for guest programs to run in, such as scratch space on disk and memory.
The Flash plug-in has now been divided into:
- Broker process: As the name says, this process takes care of the communication between the main plug-in process and the system resources and services (in case of Google Chrome, the Chrome sandbox handled this, eliminating the need of a broker process for the plug-in to be developed by Adobe). This process runs at medium integrity.
- Main Process: The main Flash process runs at low integrity mode, without complex permissions; that is, with the maximum level of security Adobe can provide making use of the features in Windows.
Does this sandboxing feature help relieve your tensions regarding Flash plug-in security? Or, would this come out to be just like Adobe Reader X sandbox which didn’t quite do what it was expected to?
[via Softpedia]

 Email article
Email article