Dropbox is an extremely popular cloud storage service used by many people, including me and likely you. However, popularity or size doesn’t mean you are immune from hackers. Since a few weeks Dropbox users have been complaining of a sudden increase in spam to e-mails that they only use for Dropbox. Dropbox has now confirmed that spam is related to a recent Dropbox security breach.
What happened is Dropbox was hacked and a bunch of usernames and passwords were stolen. One such user account belongs to a Dropbox employee and contained a file that had Dropbox users’ e-mail addresses. This document is the reason why many Dropbox users were (are?) being spammed.
Aside from the spam issue, the obvious issue at hand is the usernames and passwords of some Dropbox users were stolen. Dropbox has already contacted the affected users and informed them about the breach so they can change their passwords, and Dropbox has introduced a bunch of new security features to help prevent this from happening in the future:
- Two-factor authentication, a way to optionally require two proofs of identity (such as your password and a temporary code sent to your phone) when signing in. (Coming in a few weeks)
- New automated mechanisms to help identify suspicious activity. We’ll continue to add more of these over time.
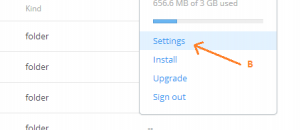
- A new page that lets you examine all active logins to your account.
- In some cases, we may require you to change your password. (For example, if it’s commonly used or hasn’t been changed in a long time)
While I understand that anyone can be hacked, it must be asked: does Dropbox store passwords in plain-text? Because, obviously, the hackers used the stolen info to login to user accounts meaning either passwords were (are) stored in a poorly protected format or were (are) stored in plain-text. What the hell Dropbox.
[via Engadget]

 Email article
Email article