Ransomware is a type of malware that locks your computers, encrypts your files, etc. to prevent you from accessing your data and asks for money if you want to regain access. In other words, your data is held ransom, hence the name ransomware.
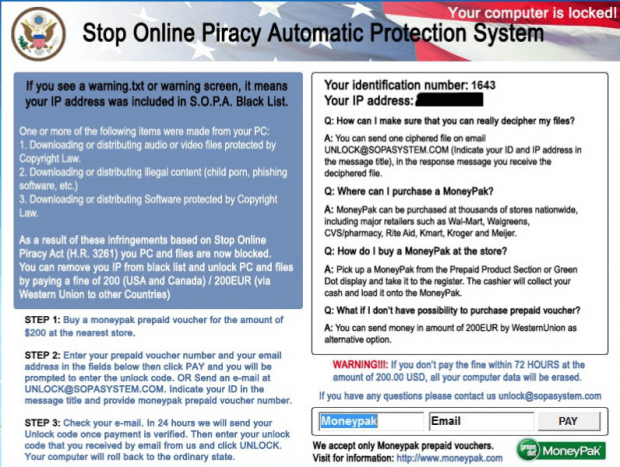
A new ransomware is floating around the internet pretending to be from the United States government, claiming the target computer has been locked because the user either illegally downloading copyrighted content, software, or child pornography. The randsomware uses the well-known but extinct Stop Online Piracy Act (the act that was never made law) as cover, claiming your computer has been put on the ‘S.O.P.A. Black List’ and your computer is being locked by the ‘Stop Online Piracy Automatic Protection System’.
In classic ransomware style, anyone affected by this ransomware is asked to make a payment of $200 within 72 hours (by purchasing a MoneyPak prepaid voucher) or else risk all their data being erased. Interestingly enough, people who don’t have access to MoneyPak stores (aka everyone outside United States and Canada — MoneyPak is a legitimate business who is unfortunately abused for these types of schemes), you can send a 200 euros through Western Union. I guess us North Americans get a discount since this is our law.
Aside from for money, the ransomware claims that users can be provided with one decrypted files as proof that the hackers can, and will, unlock your files after you pay. I wouldn’t suggest taking them up on that offer — who knows what they will e-mail you back as an attachment.
What makes this ransomware different than others is it tries to create an aura of legitimacy by pretending to the be the American government. Many people will probably think twice before giving into the demands of a ransomware attack if the attack is obvious ransomware. However, this ransomware makes it look like it is the United States government that is locking your computer, which is likely to persuade more people into giving in demands — thanks to fear or otherwise. The media attention given to SOPA/PIPA earlier this year only magnifies this effect.
It isn’t entirely clear how users are being infected by this particular ransomware but it does look like only Windows machines are being infected.
If you are infected, as with most competent ransomware, there really isn’t any way to unlock your computer unless you know how to break the encryption (which likely isn’t going to happen). It is recommended to not pay the thieves because there is no guarantee that they will actually unlock your files and they could very well simply target you again because they know you will pay. The best thing to do when infected is simply wipe your computer and restore your data from backups, assuming you have some. Once you are up and running, make sure to install the appropriate security measures — including but not limited to a competent anti-virus — and avoid shady files and websites.
[via Sophos]

 Email article
Email article