Using a PIN on your cell phone is a great way to secure you phone, data, and apps from hackers but research has found that your PINs may not secure your phone and apps as much as you think. Rather than keeping your passwords from getting into the hands of hackers, researchers have found that — by using your phone’s microphone, speaker, and camera — it’s easy to figure out what your PIN is.
Ross Anderson and Laurent Simon of the University of Cambridge have created an app, dubbed PIN Skimmer, that records the audio tones of buttons when pressed to enter PIN codes and a video from camera when entering a PIN; they can extrapolate what your PIN is from this data:
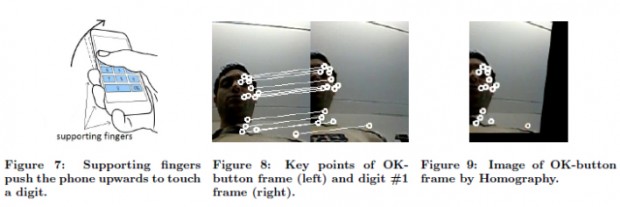
“By recording audio during PIN input, we can detect touch events. By recording video from the front camera during PIN input, we can retrieve the frames that correspond to touch events. Then we extract orientation changes from the touch-event frames, and we show that it is possible to infer which part of the screen is touched by users.”
It doesn’t take long for PIN Skimmer to obtain the PIN number either. With a traditional four number PIN, the app broke through about 30 percent of the codes within a couple attempts. It was through over half of the four digit PINs within five attempts. A longer PIN — eight digits — is more difficult to crack but 45 percent of all tested PINs were broken through within five attempts.
This isn’t just an issue for those who want to keep their personal information on their phones secure, it is also a problem for those who use secure applications on their phones, like a banking app, or use their smartphones in secure work environment. Why? Because while enterprise systems may segregate “secure” apps from “normal” apps, these apps all share the same sensors (microphone, camera, etc.) and that is what PIN Skimmer exploits.
And trust me, if these researchers can do then a malicious scumbag can, too. The worst part? The methdology behind PIN Skimmer is not operating system specific… meaning it can probably be adapted to attacked Android smartphones, iPhones, Windows Phone devices, BlackBerry phones, etc.
Moral of the story? Be careful what you install on your smartphone.
[via Gigaom]

 Email article
Email article