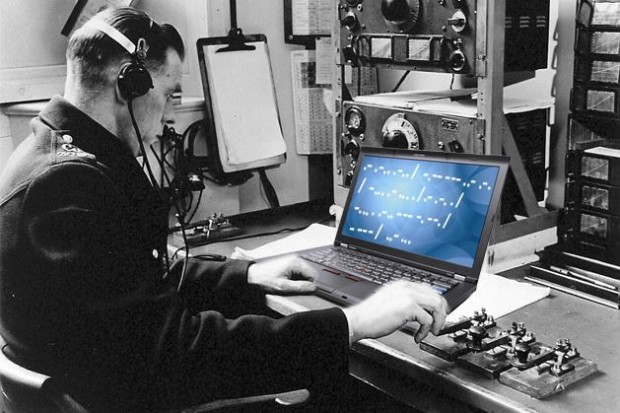
Just when you thought your computer would be safe if you kept it offline, scientists go and prove you wrong. Scientists at the Fraunhofer Institute for Communication have developed malware that can be transmitted not through a regular network, but instead through soundwaves. So far, the scientists have developed a proof-of-concept for such malware but should malware like this get out… well, you may feel like you are living in the movies.
According to the study published in Journal of Communication, the malware can be transmitted from one computer to another computer within 65 feet just by playing it through the first computer’s speakers. Like a cold can be transmitted through the air when someone coughs or sneezes, your computer can just as easily be infected by sound. The scientists have also developed a proof-of-concept that, with the construction of audio mesh, a computer can be infected even if it is outside the 65-foot perimeter.
According to Michael Hanspach, one of the authors of the study,
“The complete concept of air gaps can be considered obsolete as commonly available laptops can communicate over their internal speakers and microphones and even form a covert acoustical mesh network. Over this covert network, information can travel over multiple hops of infected nodes, connecting completely isolated computing systems and networks to each other.”
The concept is not entirely new. Some of the same techniques that these hacker-scientists use to infect a computer with an “airborne pathogen” have been used in the past to help communicate under water. However, those communications, obviously, weren’t to transmit malware. This is.
So far, researchers say that the transmission speeds are slow running at only around 20 bits per second. But that, my friends, is 20 bits per second too much sci-fi for me.
[via Ars Technica, via Journal of Communication]

 Email article
Email article