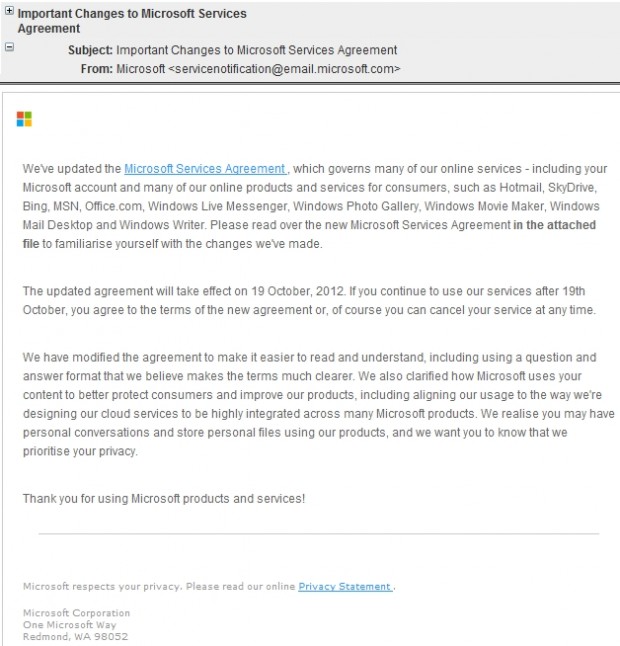
Whether it be through Windows or its online services, Microsoft touches the lives of many, many people around the world on a daily basis. So when an e-mail from “Microsoft <servicenotification@email.microsoft.com>” with the subject of “Important Changes to Microsoft Services Agreement” magically appears in the inbox of many people, my guess is they are likely to open it. Then when that e-mail tells you to view an updated services agreement via the attached PDF file, my guess is many people will open it. The kicker? The just-referenced e-mail is not actually from Microsoft and the attached file is not actually a PDF — it is a malicious EXE (Microsoft-Services-Agreement.pdf.exe) that contains malware, a backdoor Trojan (Troj/Backdr-HG) to be more specific.
What makes this malicious e-mail particularly clever is not only does it spoof a real Microsoft e-mail but it uses a real subject line to draw people in and then presents them with legitimate text in the body of the e-mail — this exact same e-mail was sent out by Microsoft in August. The only difference is the legitimate Microsoft e-mail did not contain an attached file; rather, the real Microsoft e-mail directed users to read the new agreement on Microsoft’s website.
Update: It looks like Microsoft is still sending out the legitimate version of this e-mail. So if you get an e-mail from “Microsoft <servicenotification@email.microsoft.com>” with the subject of “Important Changes to Microsoft Services Agreement”, it may be a legitimate e-mail from Microsoft or it may not be. If the e-mail has an attachment, it is a malicious e-mail and you should *not* open the attachment. If there is a link in the e-mail, the e-mail is likely legitimate but you should double-check and make sure the link is leading you to Microsoft’s website (make sure the domain is microsoft.com) and not elsewhere.
[Thanks Merlin for the heads up.]
Of course if the spam filter used by your e-mail service provider is half competent, it will immediately notice the e-mail is fake due to the e-mail not being mailed by a Microsoft server and send it to your junk or spam box. (You can spoof the e-mail header but you cannot spoof a rDNS query; rDNS is one technique used by e-mail servers to detect fake e-mails.) However, if this e-mail does somehow end up in your inbox, do not open it. And if you do open it, do not download the attachment.
[via Sophos]

 Email article
Email article