Nowadays, getting dangerous root certificates is considered a serious problem. From Dell’s eDellRoot to Lenovo’s Superfish and some different certificates that are installed by adware programs or your computer’s manufacturer or a program you installed may have added a certificate that opens you to attack. Here is a method using which you can check whether the certificates are attack free or not.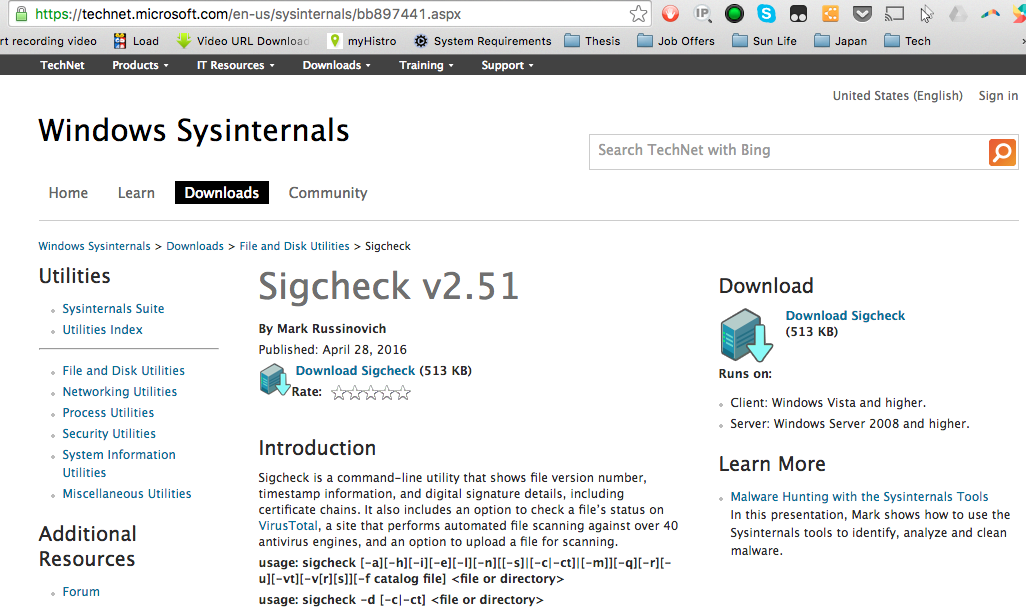
To check the certificates was not an easy process in the past. Microsoft has launched a new tool to perform the task. It will perform a quick scan on the files in your system and inform you that if any installed certificates are not trusted or secure. This tool is a good idea as it will tell you that your system is open to attack, or it saves the system from these attacks. This tool didn’t run on WINDOWS 7 before but after the updating in the tool; this will work correctly on all versions.
How to Check the Tool in your System: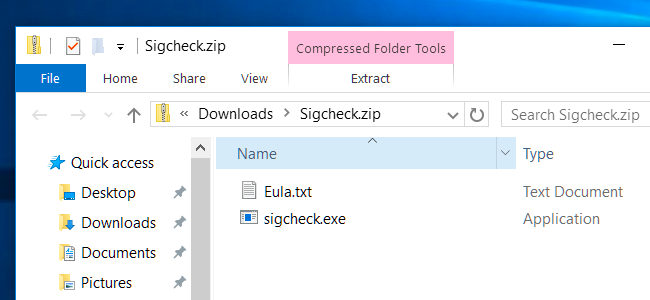
The tool provided by Microsoft is SigCheck. To get started, download this tool from the official website of Microsoft. Open the downloaded file and extract the sigcheck.exe file using an extractor as the file is zipped. Move to the folder that has the sigcheck.exe file that you have extracted. For example, if you put the file on your desktop then open the Desktop folder using File Explorer. On the keyboard, there is a key named shift press and hold on the key then right-click on the File Explorer window, and select the option of Open command window here.
Now paste or type the following command at the command prompt window and hit Enter:
Sigcheck-tv
This will download the list of certificates that are trusted by Microsoft from Microsoft and compare the list of certificates with ones that are installed on your system. If any of the certificates on your system doesn’t match to the list of trusted certificates by Microsoft, then those certificates will be mentioned in the list. If your system is clean and doesn’t contain any certificates that can cause an issue, then a message will be displayed on your screen saying No certificates found.
Found a Bad Certificate:
After running the command on your system if the sig check tool shows a list of one or more than one certificates, and you don’t have any information about them that what they are then you can search the name of those certificates on the internet and get to know about them that what are they and how they got into your system.
Removing the certificates manually is not the best idea. If an individual certificate was installed by software running on your device, then the program will reinstall the license as soon as you remove it. You need to identify the program that is the reason behind the issue, and you have to remove that program completely.
Be careful when removing certificate as there are legitimate certificates and they are part of Windows and should not be removed. So, before removing any certificate make sure that you are removing the right one.

 Email article
Email article