dotTech has gotten into the habit of warning our readers about web security issues, namely malicious emails that make their rounds in the inboxes of people around the world — such as the fake Windows Update password stealing email and the fake email from Microsoft. The following are seven new malicious emails you should avoid if you ever see them in your inbox.
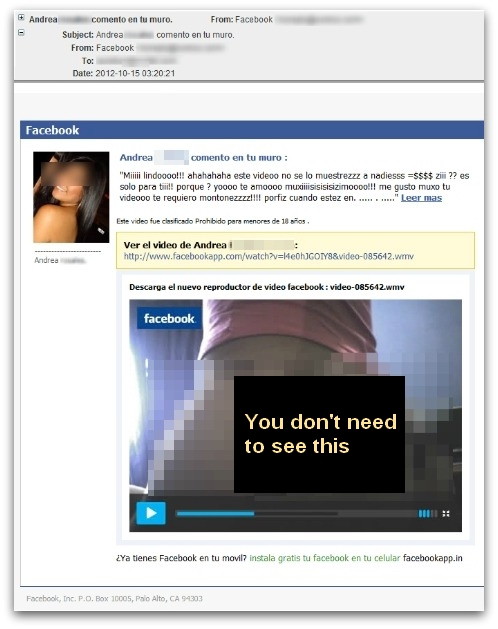
Fake Email from Facebook
This email pretends to be an email from Facebook of a couple’s conversation in Spanish. Most English readers would probably stop reading when they see Spanish but the video of the naked girl may draw in a few fools. Clicking on the link in the email doesn’t actually download a video of a naked Spanish vixen but rather downloads “Video_Multimedia.exe”, a trojan.
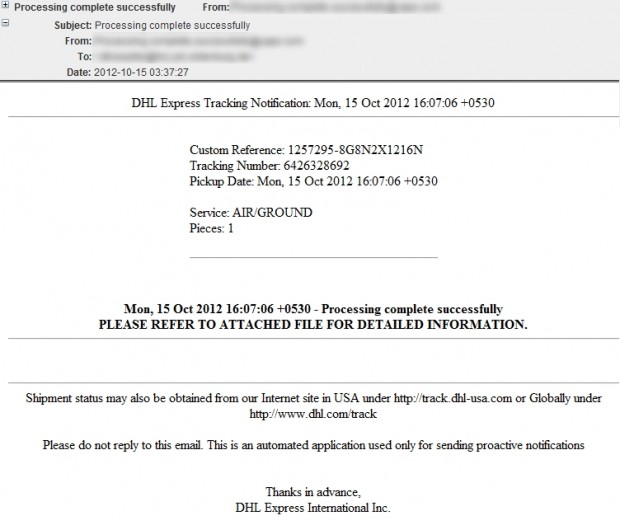
Fake Email from DHL Express
This email pretends to be from DHL, a well known package delivery and courier service. (For those dotTechies that live in the United States where DHL isn’t big, think of it like the UPS of the rest of the world.) The email lets you know that your package has been processed and you can receive more information by opening the attached file “DHL_Express_Processing_complete.pdf.zip”. If you are unlucky enough to open the file, you are infected with the trojan it holds.
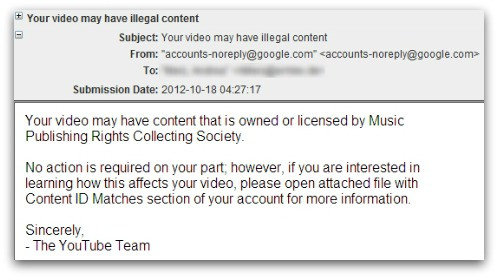
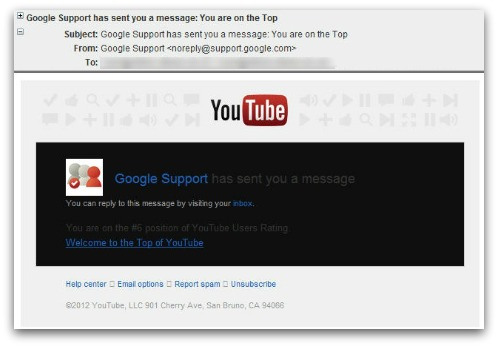
Fake Emails from YouTube
The above are actually two separate fake emails, both which pretend to be from YouTube.
The first email tells you that your YouTube video has been flagged by YouTube as containing copyright content, and tells you to open the attached file to learn more. The attached file, “Content_ID755658_Matches.zip”, contains a trojan.
The second email tells you that your YouTube video has been to the the “TOP of YouTube”, and provides you convenient links to click on. Clicking on the links redirect you to either spam websites or websites with malicious content (I don’t have enough information on the second to specify exactly where it leads).
Fake Email from Google
This fake email is similar to the previous YouTube one, pretending to tell you that your YouTube video is ranked #6 based on user ratings. This time around, however, it pretends to be from Google — not YouTube. (Technically they are the same since Google owns YouTube, but, yeah, semantics…) Like the previous email, clicking on the link provided to you redirects you to spam websites or websites with malicious content.
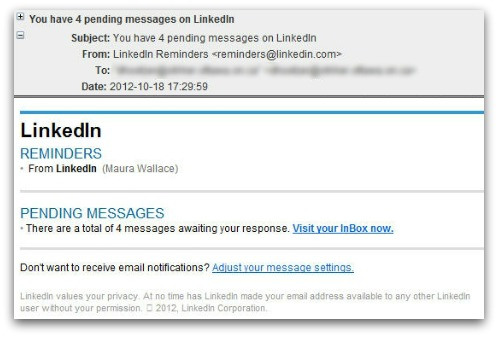
Fake Email from LinkedIn
This fake email pretends to be from LinkedIn (aka Facebook for professionals) telling you that you have new messages. The email conveniently provides you with links to click on to access your messages on LinkedIn. However, instead of sending you to LinkedIn, the links send you to spam websites or websites with malicious content.
Fake Email from British Airways
This fake email pretends to be from British Airways, letting you know of the e-ticket you just recently booked with BA. The sender of the email is kind enough to even attach the e-ticket to your email — “BritishAirways-eticket.zip”. The attachment indeed does contain a ticket… a ticket for free access to a trojan.
Conclusion
All of the emails mentioned in this article are fake, malicious emails that try to appear legitimate by spoofing their “from” address to look like it is from a company you would otherwise trust. However, further evaluation of the emails show they are clearly fake — if being in Spanish isn’t a dead giveaway then how about the grammatical and spelling errors?
In any case, any competent spam filter should automatically send these emails to the junk/spam box because of their modified headers. Still, if you do happen to see them in your inbox and you happen to open them, do not click on any links or download any attachments.
Stay safe!
[via Sophos (1) (2) (3) (4) (5)]

 Email article
Email article