Thousands of Internet users are expected to face an Internet blackout from July 9, 2012 (this coming Monday). Whom will be affected, you ask? The users who’s machines are infected by the DNSChanger malware.
Thousands of Internet users are expected to face an Internet blackout from July 9, 2012 (this coming Monday). Whom will be affected, you ask? The users who’s machines are infected by the DNSChanger malware.
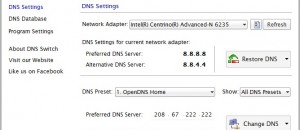
DNSChanger is a piece of malware developed by six Estonian cybercriminals. Over the past five years they have been infecting computers around the globe with DNSChanger, with an estimated four million computers infected. What DNSChanger does is it hijacks the DNS settings on computers and redirects users’ Internet browsing (web searches, website ads, etc.) to spoofed websites which contain advertisements. The more people that visit the spoofed websites and click or view the ads, the more revenue the criminals receive. It is reported that the criminals made $14 million from those ads. Not bad for five years of work, if I do say so myself.
The Federal Bureau of Investigation (commonly known as the FBI) had seized the servers of the attackers who were responsible for the DNSChanger malware, in November 2011. The FBI didn’t close down those servers entirely since that would have affected the users who were infected by the virus, i.e. shutdown their Internet access.
Since the seizure of the servers, the FBI had setup a temporary server setup with the help of a non-profit organization, Internet Systems Consortium, to provide the infected users proper time to get themselves cleaned up. The FBI has been trying to inform and alert the infected users about the malware all this time through different sources.
The servers were originally planned to be shut down on May 2012, but the action had been delayed since the number of infected users was still high during at that time. Even today, as per reports, 304,000 computers still remain infected by the malware, of which 70,000 are in the United States.
Checking whether you are infected by the DNSChanger malware is quite simple and a fix, if you are indeed infects, is also easy. To check if you are infected, simply visit the DNSChange Check-up website (link given below); the website will tell you whether you are clean or infected, without the need of any download or scan. If you find that your computer has been infected by DNSChanger, you are suggested to visit DCWG Fix section (link below) for details on how you can get yourself clean.
[via CNN Money]

 Email article
Email article