How to convert JPG images to SVG files online [Tip]
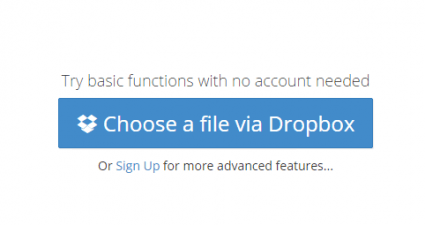
JPG images are basically raster images not vectors. So if ever you need to convert these images to vectors, you’ll need to save the file in SVG format first. The thing is it isn’t as easy as renaming the file’s extension. You’ll h...